Disclaimer: This article does not constitute legal advice. For your specific situation, we recommend consulting a lawyer specializing in data protection law.
The Procurement Guide for Data Protection Officers, IT Leaders, and Decision-Makers (2026)
You're evaluating an AI meeting tool – or you already have one in use and are wondering whether it's truly GDPR-compliant? Then you're in the right place. Choosing a tool like this is not a purely technical decision: it's a data protection decision with legal, organizational, and technical dimensions that you need to get right from the start.
AI meeting assistants that automatically record, transcribe, and summarize don't just process any data – they process spoken words. Often sensitive content from HR conversations, contract negotiations, or customer meetings. And in a format that is searchable, exportable, and potentially stored indefinitely.
This article gives you a complete, practice-tested checklist – developed on the basis of GDPR requirements, current supervisory authority recommendations, and real-world procurement experience in the DACH market.
The Most Important Points at a Glance
- A DPA is mandatory – and it needs to cover far more than a generic click-through addendum.
- Sub-processors are the hidden risk – scrutinize every service provider in the processing chain.
- AI training on customer data is a dealbreaker – get a written exclusion.
- Server location alone is not enough – support access, key management, and third-country transfers all need to be considered.
- Red flags are easy to spot – once you know what to look for.
Why Tool Selection Is So Critical
An AI meeting assistant is not an ordinary SaaS tool. What makes it different is the depth of processing: the tool doesn't just receive structured data that you consciously enter. It listens. It transcribes. It interprets. And it generates new data objects from what was said – summaries, action items, speaker labels, search indices – each of which takes on a life of its own.
What this means for GDPR: you're not dealing with a single processing operation, but with a chain of processing stages, each carrying its own requirements for legal basis, purpose limitation, access control, and deletion. Anyone who doesn't factor this in during tool selection is building in a compliance gap – one that only becomes visible at the next audit or data protection incident.
On top of that, many meeting contents touch on special categories of personal data under Art. 9 GDPR – health information in HR meetings, trade union-related content, personal circumstances. Your tool needs to be able to handle this. And you need to know how it does.
Part 1: Data Protection & Contractual Framework
Is the provider clearly positioned as a data processor?
This sounds like a given – but it isn't. Some providers try to position themselves as independent controllers in order to retain their own discretion over data use. That's a problem for you as a customer, because it means you have no authority to instruct them on how processing is carried out.
What you should check:
- Does the provider explicitly commit to processing all meeting content and derived data solely on the basis of your documented instructions?
- Is this contractually binding – and not just stated in a privacy notice on their website?
What does the Data Processing Agreement (DPA) cover?
A DPA under Art. 28 GDPR is mandatory when you use an external tool for recording, transcribing, or storing meeting content. But not all DPAs are equal. A weak DPA is barely better than none at all.
A robust DPA for AI meeting tools must cover at minimum:
- Purpose limitation for all data types: Not just for the recording itself, but explicitly for transcripts, summaries, embeddings, search indices, and metadata.
- AI training and product improvement: A clear, binding statement on whether and how customer data is used to train models or improve the product – with an enforceable opt-out or prohibition where required.
- Sub-processors: Full list of all sub-contractors, change notification obligations, and your right to object.
- Deletion and return: Concrete deletion workflows for recordings, transcripts, derived artifacts, backups, and logs – with realistic timelines and documentation obligations.
- Data subject rights: How does the provider support access and deletion requests from meeting participants who are not your employees?
- Breach notification: Notification obligation within shorter timelines than the legal maximum, plus a defined minimum content for the notification.
- Audit and evidence: What documentation will you receive – SOC 2 report, ISO 27001 certificate, penetration test summary, technical and organizational measures annex – and how frequently?
Red flag: A provider that offers no individual DPA or only provides a generic click-through addendum does not meet the minimum requirements of Art. 28 GDPR. This is a dealbreaker.
Is customer data used for AI training?
This is one of the most critical questions of all – and at the same time one where provider answers are often deliberately vague. "We don't train foundation models on customer data" sounds reassuring, but says nothing about telemetry, feedback loops, human review pipelines, or fine-tuning on aggregated data.
What you should ask and document contractually:
- Is audio, transcript, or summary content used for any purpose beyond direct service delivery to your organization?
- Are prompts, feedback, or usage telemetry fed into model training or evaluation?
- Is there human review of customer data – and if so, under what conditions and with what access controls?
Get the answers in writing – ideally as part of the DPA or as a separate data protection addendum.

Sub-processors: The Hidden Risk
An AI meeting assistant is rarely a monolithic system. Behind the visible tool there is typically a chain of service providers: a speech recognition provider for transcription, an LLM provider for summarization, a cloud host for storage, an analytics service, a support tool. Each of these sub-processors potentially processes your meeting content.
What you need to know:
- Full list of all sub-processors with the geographic location of their processing
- For each sub-processor: is a third-country transfer involved? On what legal basis?
- Do security and confidentiality obligations flow down contractually to all sub-processors?
- How will you be notified of changes to the sub-processor list – and how long is your objection window?
Practical note: "Sub-processor sprawl" – the uncontrolled expansion of the sub-contractor chain – is one of the most common compliance problems with AI SaaS providers. Also scrutinize providers who present a short sub-processor list: either the production system is genuinely lean, or the list is incomplete.
Part 2: Transparency & Operations
How are meeting participants informed?
The GDPR requires transparency towards all data subjects – not just your own employees, but also external participants, customers, and partners. The tool must support this transparency technically.
Minimum requirements:
- Automatic notification of all participants when recording starts (banner, bot announcement, or system notice)
- Ability to customize the notification text to meet German legal requirements
- Clearly visible recording indicator throughout the entire meeting
Best practice:
- Four-level transparency: policy level, invitation level, meeting level, post-meeting level (in line with the DSK's guidance on video conferencing systems)
- Documented evidence that the notification was delivered
Can recording be selectively disabled?
Not every meeting should or may be recorded. HR conversations, works council meetings, strategy sessions with heightened confidentiality requirements – all of these require granular control.
What the tool must offer:
- Recording and transcription can be disabled per meeting, per participant group, or per domain
- The default setting is "recording off" – not "recording on"
- Role-based access controls: who may start, stop, view, export, and delete recordings?
Red flag: A tool that records all meetings by default and offers no granular deactivation is incompatible with the principle of data minimization (Art. 5 para. 1c GDPR).
Who has access to recordings and transcripts?
The principle of purpose limitation applies not just to processing, but also to access. Access rights must correspond to the processing purpose – and go no further.
Questions you should ask:
- Can access rights be configured on a role basis (e.g. HR-only for HR meetings)?
- Are accesses logged – who accessed which recording, and when?
- Can individual meetings be marked as inaccessible to specific user groups?
- What access rights do the provider's support staff have to your data?
Part 3: Security & Certifications

What security evidence does the provider bring?
Security marketing is not security evidence. "We take data security very seriously" is not a meaningful statement. What you need are audited, independently verified credentials.
The relevant certifications for AI meeting tools:
SOC 2 Type II Report A SOC 2 report under the AICPA standard documents that an independent auditor has reviewed the provider's control environment – over a defined period (Type II), not just at a single point in time (Type I). For meeting tools, the most relevant Trust Services Criteria are:
- Security: access controls, logging, vulnerability management, incident response
- Confidentiality: protection of sensitive meeting content
- Privacy: alignment of data processing practices with stated notices and controls
Request the full report under NDA and review: what is in scope? Are there any exceptions? Were any controls not in place during the reporting period?
ISO 27001 Certificate ISO 27001 certifies an Information Security Management System (ISMS). It is not a product certification, but it is a strong signal of a mature security culture. Importantly: verify that the scope of the certificate covers the systems that are actually relevant to you – meaning the cloud infrastructure used for meeting recordings. A revised version (ISO 27001:2022) was published in 2022; ask about the provider's transition status.
Practical tip: ISO 27001 + SOC 2 Type II is the most robust combination for DACH procurement. That said: certifications evidence a control environment – they do not replace a GDPR-compliant legal basis, a transparency concept, or a DPA. Also, keep in mind that the AI market is relatively new and certifications like ISO take months to years. Thus, providers may have the highest data security standards even though they do not yet have the full certification (just because they are not old enough).
Encryption and Access Controls
Minimum requirements:
- Encryption of all data in transit (TLS 1.2 or higher) and at rest (AES-256 or equivalent)
- Support for enterprise identity controls: SSO (Single Sign-On), MFA (Multi-Factor Authentication), SCIM for automated user provisioning
- Least-privilege principle: every user has only the access rights required for their role
- Session logging: all access to meeting content is recorded
Advanced requirement for sensitive environments:
- Customer-Managed Keys (CMK): you hold the encryption keys yourself – the provider cannot decrypt your data without your involvement.
How does the provider handle data breaches?
Meeting content can contain credentials, trade secrets, sensitive HR information, or medical data. A data leak would potentially have significant impact. That's why not just prevention, but also response in the event of an incident, is critical.
What must be contractually governed:
- The provider's obligation to notify you within 24–48 hours of becoming aware of a breach (not only after 72 hours, as the GDPR allows you vis-à-vis supervisory authorities)
- Defined minimum content for the notification: nature of the incident, data affected, individuals affected, measures taken
- A documented incident response process – ideally evidenced through audit records or tabletop exercises
Part 4: Data Transfers & Server Location

Where is your data stored and processed?
The question of server location matters – but it is not the only question you need to ask. What counts is not just where the data resides, but who can access it and under what circumstances.
The complete transfer map you need:
- Where are recordings, transcripts, and summaries stored?
- Where does speech recognition (STT) and LLM processing take place?
- From where can the provider's support staff access production data?
- Who holds the encryption keys?
Only when you can answer all four questions do you have a complete picture of your data transfers.
EU-US Data Transfers: What Applies in 2026?
The EU-US Data Privacy Framework (DPF) has been in force since 2023 and survived an initial legal challenge in 2025. However, an appeal has been filed – and the matter is not closed (March, 2026). For your procurement decision, this means:
- The DPF is usable, but is not a "set and forget" mechanism
- Verify that the provider is actually DPF-certified (certification status is verifiable on the official DPF list)
- Ask about the contingency plan: what happens to your data if the DPF is restricted or invalidated?
- For US providers without DPF certification: on what basis (Standard Contractual Clauses, BCRs) does the transfer take place – and what supplementary measures are in place?
What Does the CLOUD Act Mean for European Companies?
The US CLOUD Act allows US authorities to compel US companies to produce data – even when that data is stored on European servers. The European Data Protection Board (EDPB) has noted that the CLOUD Act can create conflict-of-law scenarios that bypass traditional MLAT mutual legal assistance channels.
For you as a European buyer, this means: if your meeting tool provider is a US company or belongs to a US parent, "EU region hosting" alone is not sufficient protection. You must also assess:
- Which jurisdiction has legal control over the provider?
- What is the provider's policy on government requests – and do they commit to challenge, minimize, and notify you where legally possible?
- Are there technical measures (e.g. Customer-Managed Keys) that would factually prevent access even in the event of a government request?
Bottom line: For truly sensitive data, a provider headquartered and operating entirely within the EU is the most legally secure choice.
Part 5: Organizational Requirements
Do you need a Data Protection Impact Assessment (DPIA)?
Very likely yes. When an AI tool systematically records, transcribes, and evaluates communications using AI, two factors are typically present that make a DPIA mandatory under Art. 35 GDPR: the use of new technologies and the systematic processing of employee data. The DSK explicitly recommends reviewing the need for a DPIA when introducing AI tools.
A DPIA is not a bureaucratic exercise – it is the instrument with which you document, assess, and (where necessary) mitigate the risks of the tool. It is also the evidence you will need in an audit or regulatory inquiry.
How does the provider support works council requirements?
In companies with a works council, its co-determination right when introducing an AI meeting tool is mandatory (§ 87 para. 1 no. 6 BetrVG). A good provider is aware of this – and offers active support.
What you should ask:
- Can the provider technically ensure that the tool cannot be used for performance or behavioral monitoring – for example, by disabling speaker analytics?
- Are there administrative controls that can be documented in a works agreement as technical guarantees?
- Does the provider have experience with works council processes in German companies and can they contribute documentation or templates?
The Complete Checklist at a Glance
Data protection & contractual framework
- ✓ Provider is clearly positioned as data processor
- ✓ DPA is in place and covers all data types (incl. transcripts, summaries, indices)
- ✓ AI training on customer data is contractually excluded
- ✓ Full sub-processor list with locations is available
- ✓ Deletion workflows for all data types are defined and verifiable
- ✓ Support for data subject rights is contractually governed
- ✓ Breach notification within 24–48 hours is contractually fixed
Transparency & operations
- ✓ Automatic participant notification when recording starts
- ✓ Notification text is customizable
- ✓ Recording can be granularly disabled (per meeting, domain, role)
- ✓ Default setting is "recording off"
- ✓ Role-based access controls are configurable
- ✓ Access logs are available
Security & certifications
- ✓ SOC 2 Type II is available
- ✓ ISO 27001 certificate is available (scope covers relevant systems)
- ✓ BSI C5 available or mapping to C5 criteria available (where relevant for public sector)
- ✓ Encryption in transit and at rest is evidenced
- ✓ SSO, MFA, and SCIM are supported
- ✓ Customer-Managed Keys available (for highest security requirements)
Data transfers & server location
- ✓ Full transfer map is available (storage, processing, support access, key management)
- ✓ EU hosting or DPF certification evidenced
- ✓ Contingency plan for DPF invalidation is in place
- ✓ Policy on government requests is clear and contractually governed
Organizational
- ✓ DPIA has been reviewed and conducted where required
- ✓ Works council has been involved (where applicable)
- ✓ Provider supports the works agreement process
The Most Common Red Flags in a GDPR compliant Tool Selection
After reviewing many providers in the DACH market, the same warning signs come up again and again:
Refusal to disclose sub-processors
"Our sub-processors are confidential" is not an acceptable answer. Art. 28 GDPR gives you the right to be informed about all sub-contractors.
Vague statements on AI training
If a provider cannot clearly and in writing confirm that customer data is not used for training, evaluation, or product improvement, that is a significant risk.
Only SOC 2 Type I – no Type II
Type I is a point-in-time snapshot. Type II evidences operational control effectiveness over time. For production use, Type II is the relevant standard.
"EU region" as the only answer on transfers
As explained above: EU hosting without considering support access, corporate structure, and key management is not a complete transfer safeguard.
No configurable option to disable recording
A provider that doesn't offer "off by default" has not internalized the principle of data minimization.
Missing or generic deletion concepts
"Data will be deleted on request" is not a deletion concept. You need automated, documented deletion processes that apply to all data types.
FAQ – Frequently Asked Questions
Is it enough if the provider claims to be "GDPR-compliant"?
No. "GDPR-compliant" is not a certification and not a legally defined status. Any provider can claim it. What counts are concrete, verifiable measures: a DPA, sub-processor transparency, deletion concepts, security certifications.
Do we need to conduct a separate DPIA for each meeting tool provider?
Yes – provided the tool crosses the DPIA threshold under Art. 35 GDPR, which is typically the case for AI meeting assistants. If you switch providers, a new DPIA is required because the processing circumstances change.
What happens if the DPA has gaps and a data protection incident occurs?
You as the controller are liable towards data subjects and supervisory authorities – even if the fault lies with the processor. A deficient DPA also cannot shift liability to the provider. Selecting an unsuitable processor is itself a compliance violation.
Can we use a US tool if European support and data storage are located in the EU?
With caveats. Legal control by a US parent company remains a risk even with EU hosting. What matters is the combination of hosting location, support access, key management, and the provider's CLOUD Act exposure. A sound risk assessment and documented supplementary measures are required in any case.
How often should we re-evaluate an existing provider?
We recommend annually – or on an event-driven basis: changes to the sub-processor list, new product features with data protection relevance, changes to the transfer framework (e.g. DPF developments), or following a data protection incident.
Conclusion: Compliance Starts Before You Sign
The decision to adopt an AI meeting tool is one of the most far-reaching data protection decisions a company can make. It affects not just internal processes, but every person who ever participates in a meeting – employees, customers, partners.
Working through this checklist thoroughly protects your organization from fines and reputational damage. But it also leads to a better product decision: providers who meet the highest standards on data protection and security tend to be more reliable across other quality dimensions too.
How Sally Meets This Checklist
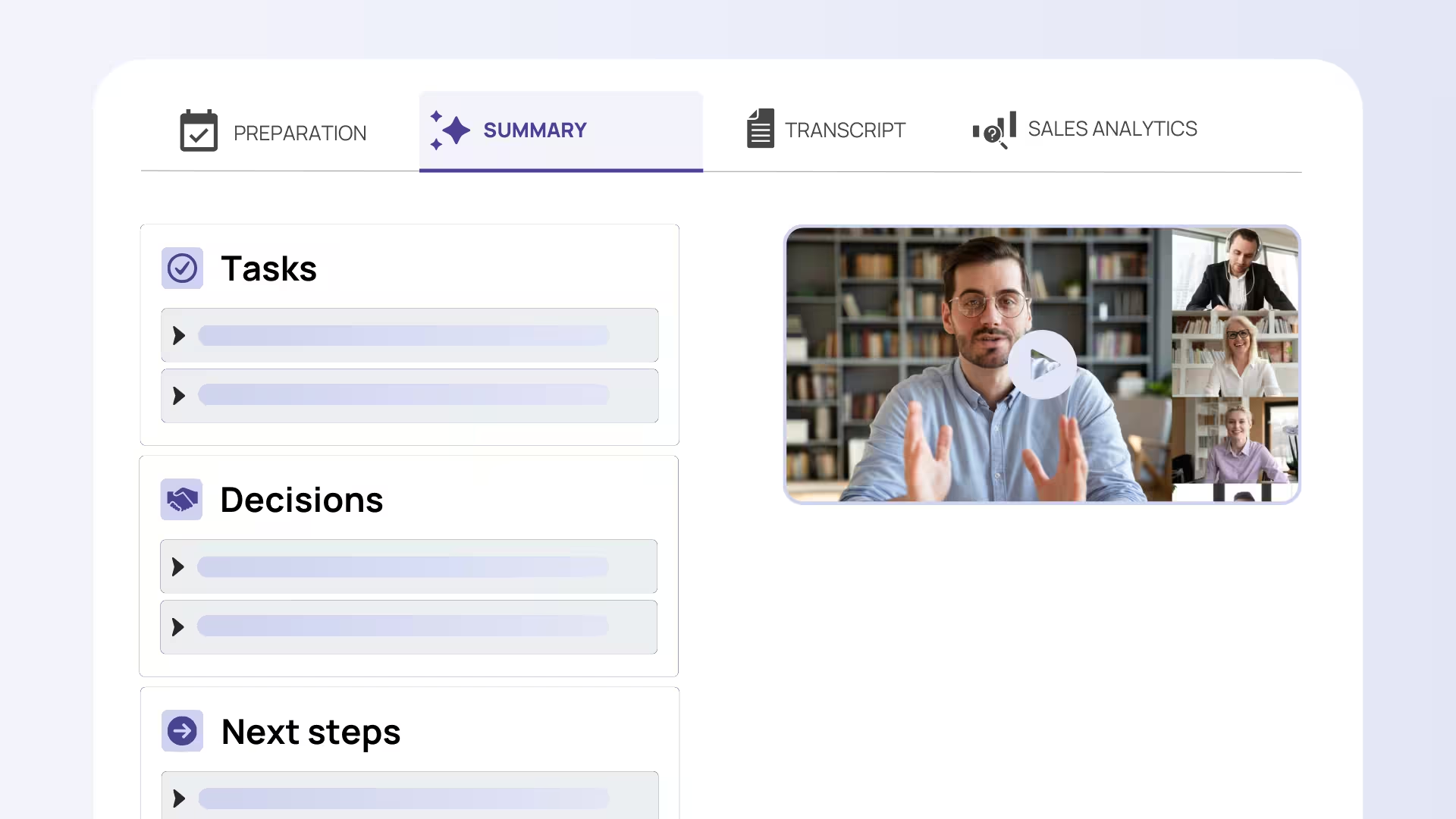
Sally is an AI meeting assistant with it's headquarter in Germany and was orginally built in cooperation with a big German corporation – with the conviction that every one of these requirements should be treated not as a compliance obligation, but as a product decision:
- ✓ Clear positioning as data processor | DPA included | full sub-processor transparency
- ✓ AI training on customer data contractually excluded
- ✓ Servers in Germany and EU | no US corporate structure | no CLOUD Act exposure
- ✓ Automatic consent notification | configurable deletion periods | off by default
- ✓ Role-based access controls | SSO & MFA | access logs
- ✓ SOC 2 in preparation | ISO 27001 in preparation (we have a certificate) | BSI alignment
Disclaimer: This article does not constitute legal advice. For your specific situation, we recommend consulting a lawyer specializing in data protection law.




